Phishing attacks have reached unprecedented levels, increasing 600% since 2021 during a pandemic and becoming the main mode of cyber infection. Deceptive tactics used by cybercriminals represent an imminent danger to individuals and organizations alike by adopting false identities to lure unsuspecting victims into sharing sensitive data through emails, websites, messages, or SMS. Join us as we unravel this growing threat by delving deeper into its intricate workings to build more resilience against future phishing attempts.
What is Phishing?
Phishing, derived from the term "fishing," lures unsuspecting individuals into divulging sensitive information from a vast pool of users. These cybercriminals, known as "phreaks," employ deceptive tactics to trick victims.
To carry out their malicious intentions, phishers adopt various personas and create fabricated emails, messages, or websites that exude an air of trustworthiness. They skillfully imitate familiar figures such as family members, high-ranking executives, or prominent public figures, exploiting our inherent trust and willingness to assist others. Through these manipulative techniques, they coerce individuals into inadvertently sharing private data.
The fraudulent emails, messages, or websites in these schemes bear striking resemblances to legitimate counterparts, often imitating reputable organizations, banks, or government agencies. Meticulously crafted with meticulous attention to detail, they are painstakingly designed to be virtually indistinguishable from genuine communications. Leveraging psychological tactics, phishers exploit our fears, create a sense of urgency, or entice us with irresistible offers, overriding our rational judgment. Consequently, we find ourselves enticed into clicking malicious links, downloading harmful attachments, or unknowingly engaging in fraudulent transactions.

Once victims succumb to the trap and click on the provided link, they are redirected to fake websites that convincingly replicate the authentic platforms. At this critical juncture, victims are prompted to enter their login credentials or personal information, unwittingly surrendering their sensitive data to nefarious actors. The repercussions of such actions can be catastrophic, resulting in identity theft, financial losses, and irreparable harm to one's reputation.
Types of Phishing Attacks
This article section contains a comprehensive breakdown of the primary types of phishing attacks and their origins.
A. Email Phishing
Email phishing is one of the most prevalent phishing attacks. In this attack, perpetrators craft messages that closely resemble legitimate emails from well-known companies, banks, or government offices. These fraudulent emails trick recipients into taking action that benefits the attackers. Victims are often prompted to click on links, download attachments, or even send money. In addition, attackers exploit emotions such as fear or urgency to override the victims' judgment and increase their chances of success.
When a victim clicks on the provided link in a phishing email, they are redirected to a counterfeit website that appears genuine. On this fake website, the attackers aim to harvest the victim's login credentials or other sensitive information. The unsuspecting victim may enter their username and password, unknowingly handing over their data to the attackers. This can lead to severe consequences, including identity theft, financial loss, and compromised online accounts.
B. Vishing, Smishing, and Catfishing

Phishing attacks have extended beyond email to other communication channels. Vishing, short for voice call phishing, involves attackers impersonating legitimate entities through phone calls. For example, they may pretend to be from a bank, a customer support service, or another trusted organization. The goal is to manipulate the victim into revealing confidential information, such as account numbers or passwords, over the phone.
Smishing targets mobile devices through SMS or text message phishing. Attackers send deceptive messages to users, often containing malicious URLs or requests for sensitive information. By exploiting the immediacy and trust associated with text messages, they aim to deceive individuals into divulging their data or clicking on harmful links.
Catfishing takes a different approach by exploiting individuals for romantic purposes. In these cases, attackers create fake online profiles, often on dating websites or social media platforms, to deceive unsuspecting victims emotionally. They establish a relationship and gain the victim's trust before manipulating them into sharing personal information or even sending money.
C.Spear Phishing and Whale Phishing
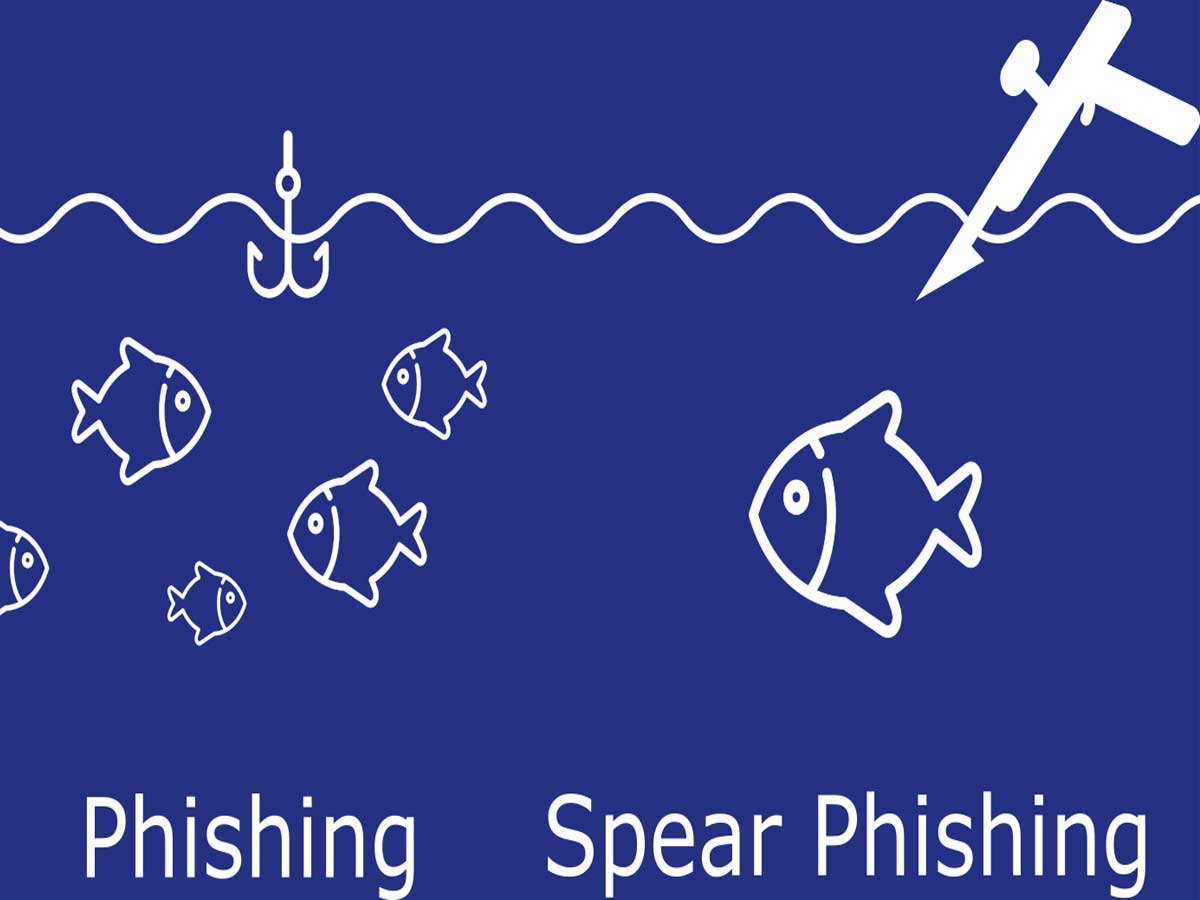
Spear phishing represents a more targeted and sophisticated form. Attackers conduct extensive research on their victims to create personalized and credible attacks. By tailoring their messages to specific individuals or organizations, they increase the likelihood of success. For example, an attacker may gather information from social media profiles or publicly available data to craft an email that appears to be from a colleague or a trusted contact. This level of personalization makes it more challenging for victims to recognize the fraudulent nature of the communication.
Whale phishing, or "big game hunting," focuses on high-profile individuals who possess valuable assets, such as executives, celebrities, or individuals with substantial wealth. Attackers invest time and effort into studying their targets, understanding their routines, and exploiting their vulnerabilities. By gaining unauthorized access to the accounts or networks of these prominent individuals, attackers can potentially access sensitive information or carry out fraudulent activities on a larger scale.
D.Clone Phishing
Clone phishing involves the creation of replicas of legitimate websites to deceive individuals into entering their credentials or personal information. Attackers often use previously sent emails or other forms of communication as a basis for cloning the website. By making slight modifications, such as replacing legitimate links with malicious ones, attackers trick victims into believing they are interacting with a trusted source. This type of phishing attack capitalizes on familiarity and the trust individuals place in previously received communications, making it more difficult to detect the fraudulent nature of the cloned website.
Evolution of Phishing Attacks
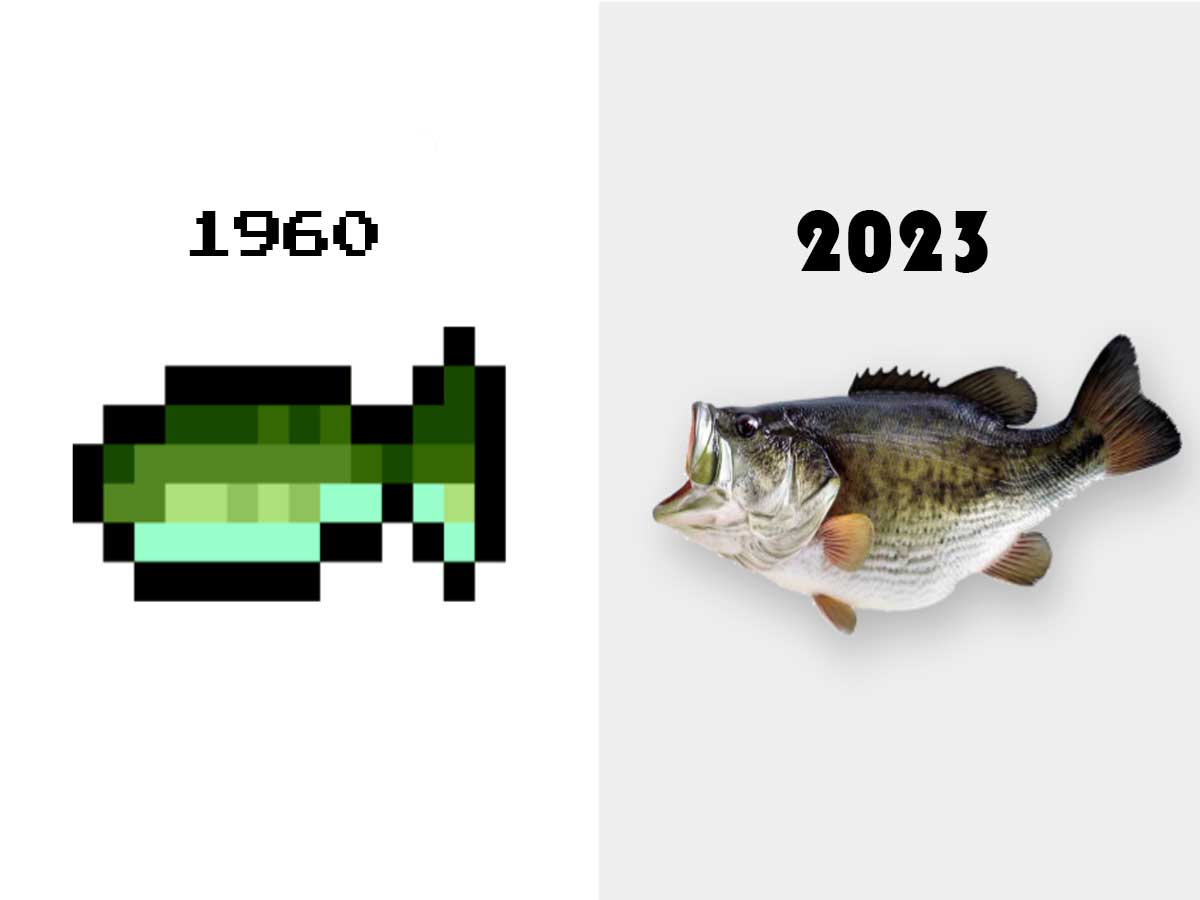
During the 90s, AOL emerged as a highly popular internet service provider, attracting millions of customers. Unfortunately, this popularity did not go unnoticed by hackers who saw an opportunity to exploit AOL's user base. The Warez community, a group involved in the distribution of pirated and illegal software, found AOL to be a convenient platform for their activities. This community played a significant role in the early stages of phishing, a cybercrime technique aimed at tricking individuals into sharing sensitive information.
Initially, the Warez community targeted AOL users, stealing their usernames, passwords, and personal information. With this ill-gotten data, they developed an algorithm that allowed them to generate random credit card numbers. These counterfeit credit card numbers served multiple purposes, including the creation of new AOL accounts and the malicious act of spamming other AOL members. Recognizing the severity of the situation, AOL took action to enhance its security measures and combat this emerging phishing threat.
The term "phishing" was first used and recorded on January 2, 1996, according to Internet records.
As AOL bolstered its security defenses, hackers adapted their tactics and shifted towards impersonation attacks. Leveraging AOL Messenger, they crafted spoof emails, posing as AOL employees, with remarkable attention to detail. The fraudulent emails closely mirrored the appearance of genuine AOL communications, replicating colors, fonts, and text styles. Within these deceptive messages, hackers would request individuals to verify their AOL accounts and provide personal information. Tragically, many unsuspecting AOL users fell victim to this ruse, unaware of the malicious intent behind the emails.
The situation escalated further as hackers created new AIM (AOL Instant Messenger) accounts that were immune to bans or suspensions imposed by AOL's Terms of Service department. This allowed the attackers to continue their nefarious activities unhindered. Recognizing the gravity of the situation, AOL took action by sending warning messages and emails to its customers, urging them to exercise caution and refrain from disclosing personal information through email and messenger platforms.
With the advent of eCommerce and online payment systems, hackers redirected their attention towards these lucrative targets. In June 2001, the E-Gold website became the victim of the first known phishing attack on an eCommerce platform, although it proved unsuccessful. Undeterred, hackers registered numerous domains resembling popular sites like eBay and PayPal in 2003. They then employed illicit worm software to send spoof emails to unsuspecting customers of these platforms. Tricked by the authenticity of these phishing emails, customers unknowingly provided their credit card details and other personal information, falling prey to the attackers' schemes.
By early 2004, phishing had evolved into a highly profitable business for hackers, leading them to target banks, enterprises, and their customers. Popup windows became one of the primary tools utilized by cybercriminals to gather sensitive information from unsuspecting users. Over time, hackers continually refined and expanded their techniques, introducing methods like spear phishing, vishing (voice call phishing), smishing (SMS/text message phishing), keylogging, and content injection to maximize their success rates in carrying out phishing attacks.
Recognizing and Protecting Against Phishing Attacks

Identifying phishing attempts can be daunting, but being aware of certain red flags can significantly enhance your defenses. Here are some telltale signs to watch out for:
- Offers That Seem Too Good to Be True: Phishing emails often promise irresistible deals or opportunities that sound too good to pass up. Exercise caution when encountering such offers, and be skeptical of anything that appears overly enticing.
- Emails from Unfamiliar Senders: If you receive an email from an unknown sender, especially one that requests personal information or urges immediate action, proceed cautiously. Legitimate organizations typically have established communication channels, so be wary of unexpected messages.
- Scary Messages Urging Immediate Action: Phishers use fear tactics to manipulate their victims. Beware of messages that create a sense of urgency or threaten dire consequences unless you take immediate action. Genuine institutions usually handle important matters through more official channels.
- Unexpected Attachments or Suspicious Links: Exercise extreme caution when encountering unexpected email attachments or hyperlinks. These can lead to malicious websites or trigger a malware download onto your device. Always verify the authenticity of the source before interacting with any attachments or links.
Protective Measures

To safeguard yourself against phishing attacks, it is essential to implement the following protective measures:
- Avoid Opening Emails from Unfamiliar Senders: If an email appears suspicious or is from an unknown source, it's best to refrain from opening it. Deleting such emails reduces the risk of falling victim to phishing attempts.
- Refrain from Clicking on Unknown Links: Instead of clicking on links provided in emails, manually navigate to websites by typing the URL directly into your browser. This ensures that you are accessing an authentic website, not a fraudulent one.
- Check for Secure URLs (HTTPS): Before entering sensitive information, always verify that the website's URL begins with "HTTPS" instead of just "HTTP." The "S" signifies a secure connection, adding an extra layer of protection.
- Utilize Antivirus/Anti-Malware Software: Installing reliable antivirus and anti-malware software on your devices provides an additional line of defense against phishing attacks. These tools can detect and block suspicious activities, safeguarding your data and online activities.
Phishing on Mobile Devices

The widespread adoption of smartphones, tablets, and mobile apps in our daily lives has turned these devices into indispensable tools we depend on. However, this heavy reliance also exposes us to an elevated risk of falling victim to phishing attacks by hackers.
When dealing with phishing emails, computer users enjoy the advantage of hovering over links and carefully examining the URLs for any signs of malicious intent. Unfortunately, displaying URLs on mobile devices is not as straightforward, making it more challenging to identify phishing attempts effectively.
The landscape of phishing campaigns has undergone significant changes. While email used to be the primary conduit for such attacks, its dominance has dwindled to 15% of incidents since 2017. Instead, mobile applications have taken the lead as the favored platform for phishing attempts. Unfortunately, mobile phones often lack built-in filtering and spam detection features, exposing users to incoming messages regardless of their content.
Phishing campaigns have expanded their reach beyond emails, now exploiting the native SMS, MMS, and messaging functionalities found in popular mobile apps. Cybercriminals target users of social networks, games, news, and travel apps, sending deceitful messages that entice victims with tempting offers or urgent requests. These messages typically consist of concise content, compelling calls-to-action, and malicious URLs cleverly disguised as legitimate communication.

The emergence of smishing, a sub-category of phishing, underscores the sophistication of attacks conducted through native mobile messaging applications. As users increasingly rely on their mobile devices for various activities, it becomes imperative to bolster security measures. This entails educating users, developing secure mobile apps, and implementing robust anti-phishing technologies tailored to the mobile ecosystem.
Impacts of Phishing Attacks
Phishing attacks have wide-ranging consequences that go beyond individual victims. In the corporate realm, these malicious tactics account for 32% of data breaches. The impact is severe, resulting in negative publicity, legal implications, and significant financial losses for affected organizations. Moreover, rebuilding a damaged reputation can take years, eroding the trust and confidence of customers.

The extent of the phishing problem is alarming. Every month, many new phishing websites emerge, specifically designed to deceive unsuspecting individuals. Even more worrisome is that 68% of these fraudulent sites utilize HTTPS, a security protocol typically associated with trustworthy websites. This crafty approach adds more credibility to these deceitful platforms, making it even more challenging for users to differentiate between legitimate and malicious websites.
While raising employee awareness and implementing training programs are vital in reducing the risk of falling prey to phishing attacks, they need to be more foolproof. Despite educational efforts, a troubling statistic reveals that 2% of employees still click on phishing links daily. This underscores organizations' ongoing challenge in combating human error and fostering a robust security culture throughout their workforce.
In a connected world, phishing attacks pose a constant threat. Stay vigilant, recognize the signs, and protect yourself. Safeguard your information, double-check URLs, and be cautious of suspicious links. With knowledge and proactive measures, you can outsmart the phishers. Stay safe and secure in the digital realm. You've got this!
Sources: leviathansecurity.com / thehill.com / malwarebytes.com / pradeo.com / verizon.com / phishprotection.com / phishing.org / cisco.com